7 Genius Ways to Download Snapchat Videos (No One Tells You About!)
Introduction
Let’s be honest — if you’ve ever searched for snapchat video download, you’ve probably realized it’s not as straightforward as saving a picture from your gallery. Snapchat was designed to make content temporary, but sometimes you just need to keep that hilarious snap from a friend or save your own story before it disappears. Whether you’re looking for a way to download Snapchat video on your phone, a quick snapchat download video hack, or a reliable video download for Snapchat, this guide will walk you through the smartest and safest methods.
And here’s the twist — I’m not going to bore you with just the basics. I’ll show you 7 genius ways to download Snapchat videos that most people don’t even talk about, plus tips, examples, and some real-life scenarios where each method makes sense.
Find More: 7 Best Snap Story Viewer Apps to Watch Stories Anonymously
Why People Search for Snapchat Video Download Methods
There are plenty of reasons people look for these hacks:
- Maybe a friend sent you a snap that made you laugh so hard you want to keep it forever.
- Maybe you shared a story that you forgot to save before it expired.
- Or maybe you’re a content creator who wants to repurpose your Snapchat videos for TikTok, Instagram Reels, or YouTube Shorts.
Some people even use Snapchat as a quick video editor because of its filters, and then wonder how to pull that content out of the app for later use. Whatever the case, you’re not alone — people search “download Snapchat videos” millions of times every year.
Is It Legal and Safe to Download Snapchat Videos?
Before diving in, let’s clear this up. Saving your own content? Totally fine and encouraged — Snapchat even makes it easy. Saving someone else’s snaps without permission? That’s where things get tricky. Always respect privacy and use these methods responsibly.
Also, beware of sketchy apps and sites that promise you free downloads but might be hiding malware. Later in this article, I’ll share how to avoid those pitfalls so you don’t end up compromising your account or your phone.
Now that’s out of the way — let’s get into the good stuff.
7 Genius Ways to Download Snapchat Videos (No One Tells You About!)

1. Use Snapchat’s Built-in Save Feature (For Your Own Videos)
The easiest way to download Snapchat videos is already built into the app.
- Record a snap → Tap the save button → It goes straight to your Memories or Gallery.
- For Stories, tap the three dots → “Save Story.”
When it’s best: Perfect for saving your own creations, stories, or funny snaps you want to share again elsewhere. If you’re making content for multiple platforms, this built-in save feature is your best friend.
Limitation: This only works for your own snaps, not someone else’s. But if you’re building a brand or want a personal archive, this method is golden.
2. Screen Recording Apps for Snapchat Video Download
One of the most popular hacks is using a screen recorder.
- On iPhone: iOS has a built-in screen recorder (swipe down → tap the circle).
- On Android: Most phones now include native screen recorders, but if not, apps like AZ Screen Recorder do the job.
Pro Tip: Snapchat used to notify users if you screen-recorded. On some devices, it still can. Test it with a friend before recording secretly.
Why it’s genius: You can capture anything — videos, chats, even disappearing snaps. Plus, once you have the screen recording, you can trim and edit it down to just the piece you want.
When it shines: If you need a quick solution and don’t want to bother with third-party apps, screen recording is universal and always accessible.
3. Online Snapchat Video Download Tools
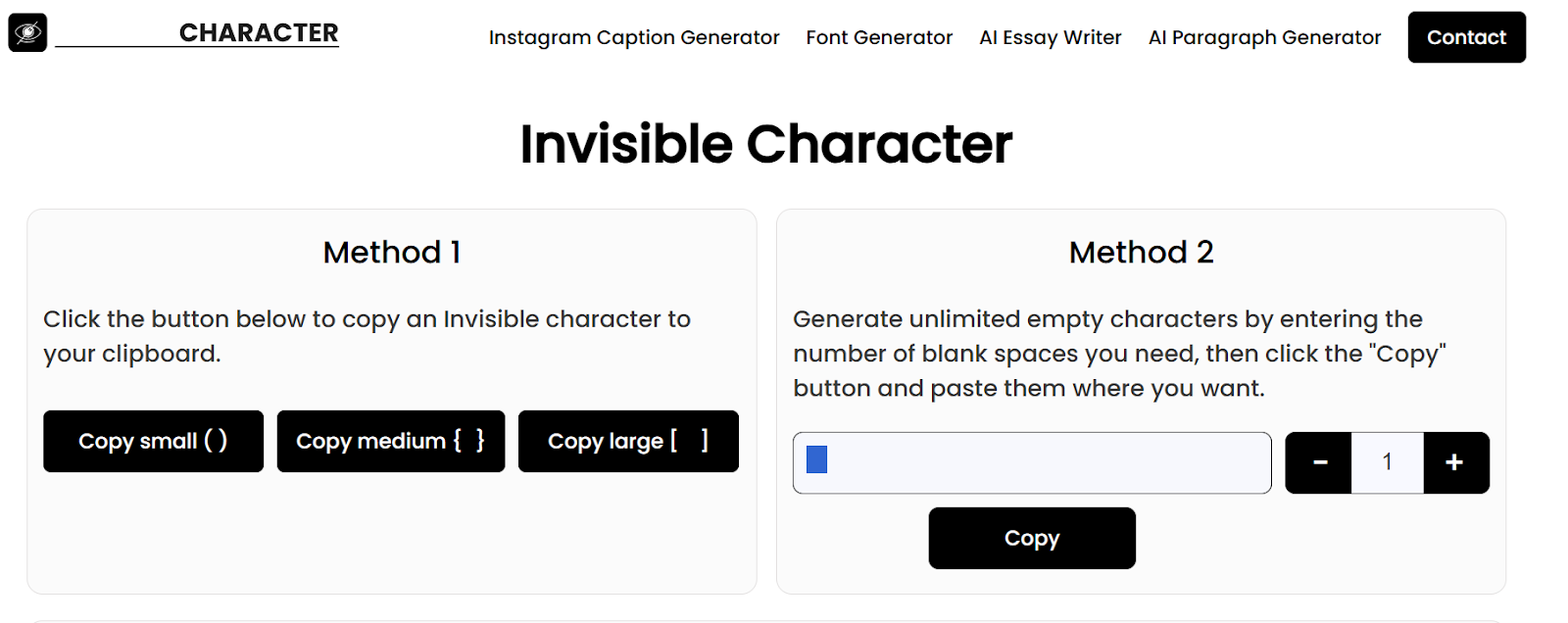
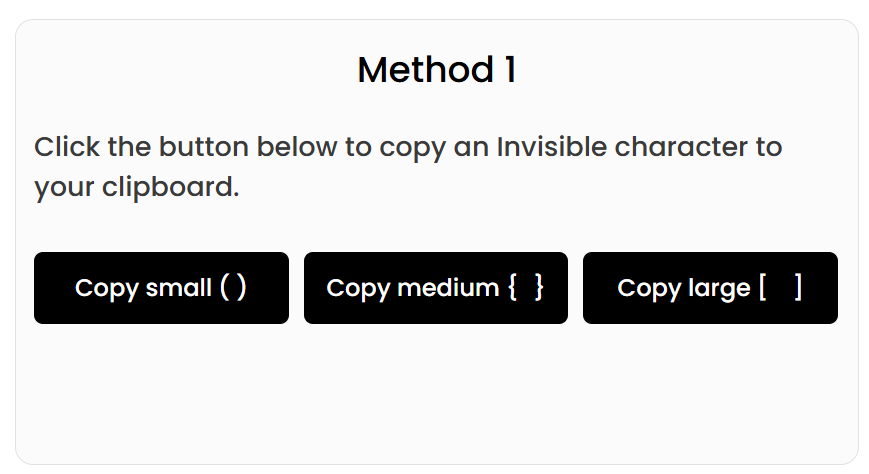
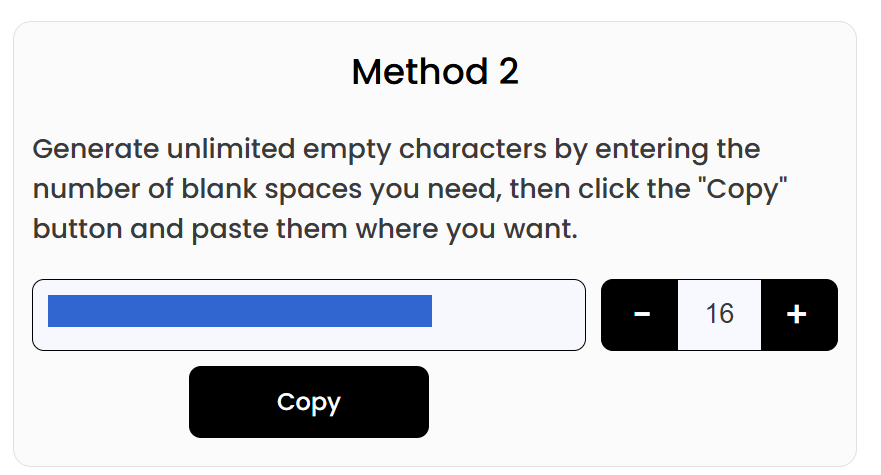
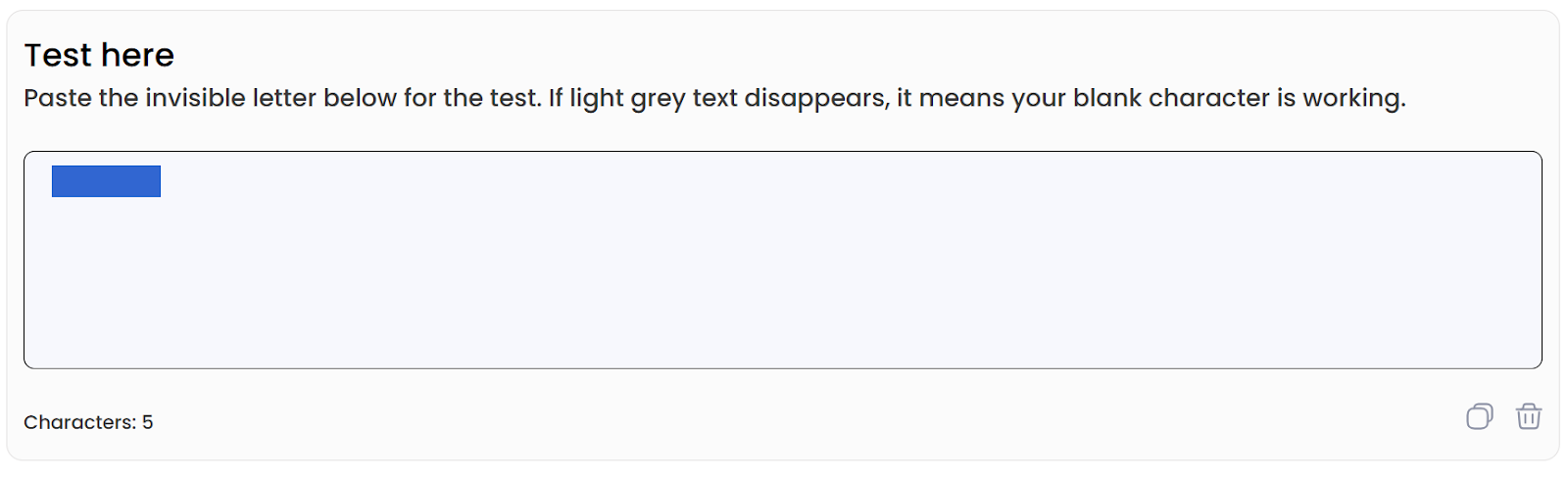
If you want a quick, no-fuss option, there are online tools made just for this. Simply paste the link of the snap (if it’s shareable) into a snapchat download video site and hit download.
- Example tools: SnapSave, SaveSnap, and similar.
- Works for both stories and spotlight videos.
Pros: Super quick, no installation needed, and many are free.
Cons: Not all sites are trustworthy. Stick to reliable ones to avoid sketchy ads or malware. Always use a secure browser.
Who it’s for: People who don’t want to clutter their phone with new apps and just need a one-time solution.
4. Third-Party Snapchat Saver Apps
Yes, there are dedicated apps that let you download Snapchat videos. They usually work by linking with your account and saving snaps in real time.
- Examples: Casper (older but still around), SnapSave for Android, and some iOS apps.
- They let you download without the other person knowing.
Risks: Using third-party apps can get your account flagged or even banned. Be cautious and only use trusted apps that have good reviews and updated versions.
When useful: If you regularly want to save snaps (like if you manage a content account and need constant access), these apps can be convenient. Just weigh the risks carefully.
5. Snapchat Video Download on PC or Mac
If you prefer using a computer, this method is gold.
- Install a screen recorder for desktop (like OBS Studio or Camtasia).
- Open Snapchat on your PC using an emulator (like Bluestacks) or Snapchat’s web version.
- Record or save videos directly.
Bonus: Some browser extensions also let you save snaps, though they can be hit or miss. Always test with non-important snaps first.
Why it’s awesome: Larger storage, better organization, and easier editing. If you’re making compilations or using snaps for professional projects, saving them on a PC gives you more control.
6. Using Cloud Storage for Snapchat Downloads
Sometimes the smartest trick isn’t obvious. Save your own snaps directly to the cloud:
- Set Snapchat to automatically save to Memories & Camera Roll.
- Sync your gallery with Google Drive, iCloud, or Dropbox.
Now your Snapchat videos are safe forever, even if you switch phones or lose your device.
Why it’s genius: No need to worry about losing your videos if you delete the app or run out of storage. Plus, you can access your snaps from any device, anywhere in the world.
When to use: If you’re someone who creates a ton of content and doesn’t want to constantly transfer files, automatic cloud backups are a lifesaver.
7. Advanced Methods: File Manager Tricks
This one’s for the tech-savvy.
- On Android, open a File Manager app.
- Navigate to “Android → Data → com.snapchat.android → Cache.”
- Some unsaved videos may still be stored there temporarily.
Heads up: This doesn’t always work and files may be corrupted, but when it does, it feels like magic. It’s almost like finding hidden treasure in your phone.
When helpful: If you accidentally closed Snapchat before saving a video and it hasn’t been fully cleared from your cache yet.
Conclusion
So there you have it — 7 genius ways to download Snapchat videos. From simple built-in features to advanced tricks like file managers, there’s a method for everyone.
- Want quick and easy? Use Snapchat’s save button or a screen recorder.
- Want flexibility? Try online tools or saver apps.
- Want long-term storage? Sync everything to the cloud.
At the end of the day, the best video download for Snapchat method is the one that fits your needs without compromising safety or privacy. Some methods are beginner-friendly, while others are for power users who want total control.
If you found this useful, try one of these methods today, experiment with different approaches, and never lose a snap again.
Find More: Boost Your Sales With SEO Services
FAQs
1. Can I download Snapchat videos without them knowing?
Yes — screen recording or third-party apps can do this. But always respect privacy and think twice before saving someone’s content without consent.
2. Are third-party Snapchat download apps safe?
Some are, some aren’t. Always research before using them, read reviews, and avoid shady apps that ask for too many permissions.
3. How do I download someone else’s Snapchat story?
You can use online tools, screen recording, or saver apps. But again — only with permission. It’s better to ask first.
4. Can I save Snapchat videos to my gallery automatically?
Yes! Change your settings to save every snap to your camera roll. Combine that with cloud storage for a seamless archive.
5. What is the easiest method for Snapchat video download in 2025?
The easiest? Screen recording. The most reliable? Saving directly to your Memories & Camera Roll. The smartest? Setting up cloud backups so you never think about it again.