10 Best Free FLV to MP3 Tools That Actually Work in 2025
Introduction
FLV to MP3 conversion is still one of those things people search for all the time. Maybe you’ve got an old .flv video file from YouTube or a lecture you downloaded years ago, and you just want the audio without the bulky video. Or maybe you’re trying to save music, podcasts, or voice clips for offline listening. Whatever the reason, a good FLV to MP3 converter makes life easier. The tricky part? Not all tools work well, and some promise a lot but deliver junk quality, or worse, spammy ads that waste your time.
In this article, we’ll cover the 10 best free FLV to MP3 tools that actually work in 2025. We’ll also dig into why FLV is still relevant, what features matter most in a converter, and how to avoid common mistakes. I’ll share personal tips, highlight what to avoid, and answer the most common questions about converting FLV to MP3 so you can do it confidently.
Find More: 7 Fastest MKV to MP3 Converters That Actually Work
What Is FLV and Why Convert It to MP3?
Understanding the FLV Video Format
FLV stands for Flash Video. It was once the standard for streaming video content online, especially in the early days of YouTube, DailyMotion, and similar platforms. Even though Flash has been officially discontinued, many people still have old FLV files saved on their hard drives or in cloud storage.
The Advantages of Extracting Audio from FLV Files
Sometimes, you don’t need the video — just the sound. Converting .flv to mp3 helps you:
- Save storage space by stripping away video data you don’t need.
- Listen offline on any device that supports MP3, from smartphones to car stereos.
- Build playlists for study, workouts, relaxation, or entertainment.
- Share audio clips more easily since MP3 is more universally supported than FLV.
Common Use Cases for FLV to MP3 Conversion
- Downloading music tracks from FLV video files.
- Converting lectures, tutorials, or audiobooks into portable audio.
- Extracting soundtracks or sound effects from FLV videos for creative projects.
- Saving the spoken parts of interviews, webinars, or podcasts.
Key Features to Look for in a Free FLV to MP3 Converter
Speed and Performance
Nobody likes waiting around. The best converters handle large files quickly without crashing. A good balance of speed and reliability makes a world of difference.
Audio Quality Retention
One of the biggest concerns is losing quality during conversion. A good converter should let you choose bitrates (like 128kbps, 192kbps, or 320kbps) so you get the sound quality you want.
Ease of Use
Not everyone is tech-savvy. A tool with a simple drag-and-drop interface or a straightforward upload button saves frustration. The fewer clicks, the better.
Cross-Platform Compatibility
The best flv to mp3 converter online should work across devices — Windows, Mac, Linux, and even smartphones. Bonus points if it supports cloud imports from Google Drive or Dropbox.
Security and Privacy
This part is overlooked often. If you’re uploading private or sensitive files, you want a site or software that doesn’t keep your data. Pick tools with clear privacy policies.
10 Best Free FLV to MP3 Tools That Actually Work in 2025
Here’s the good part: the real tools you can count on. All are either free or freemium and tested to work this year.
1. OnlineVideoConverter – Best Overall Free Converter
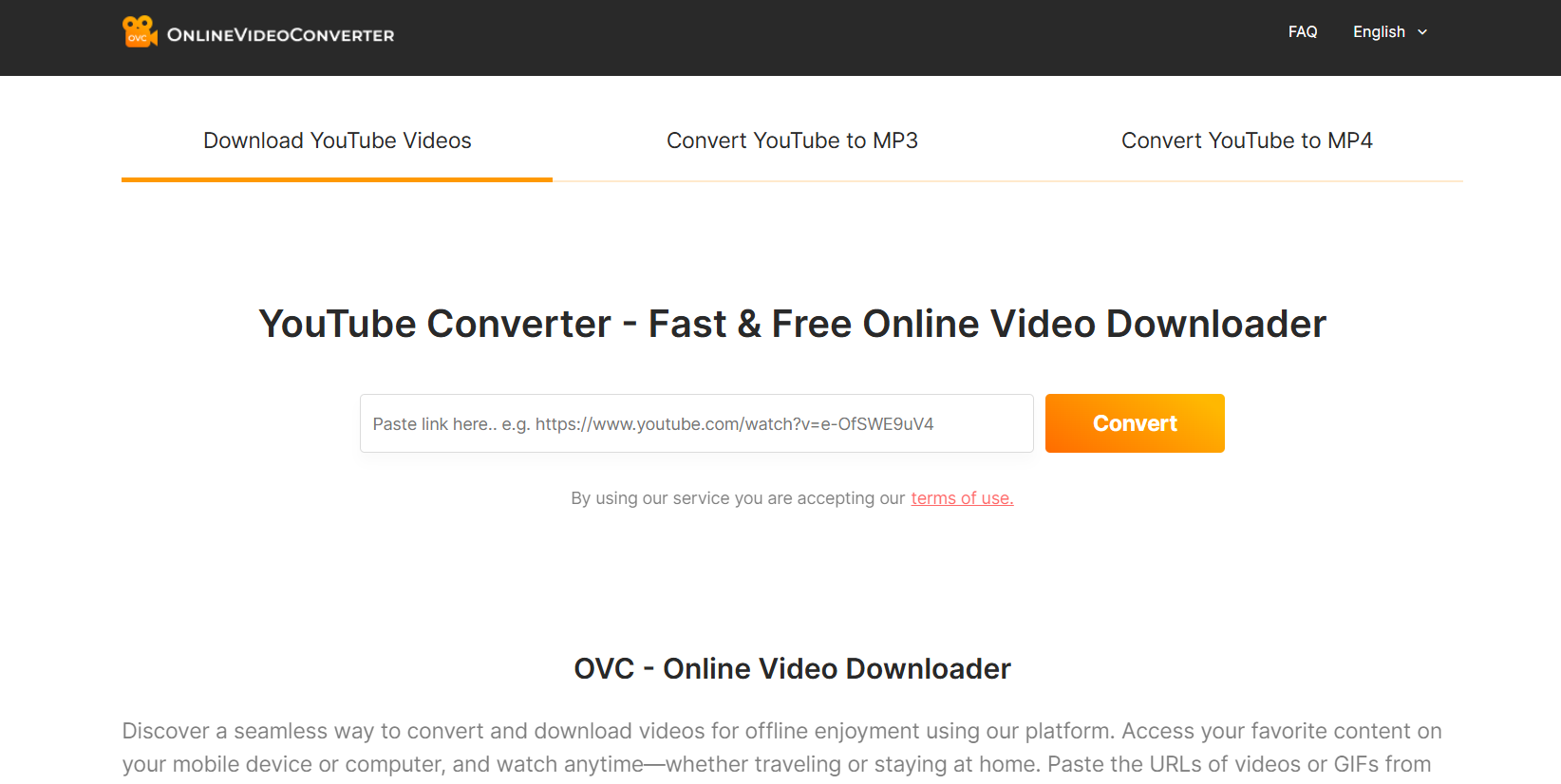
This classic online converter still works great in 2025. It’s fast, free, and doesn’t need downloads. Perfect for quick conversions when you don’t want to install extra software.
2. Any Video Converter Free – Best for Desktop Users
A trusted desktop app that handles FLV to MP3 plus almost every other format. Works offline, supports batch conversions, and even lets you tweak audio settings.
3. VLC Media Player – Best Hidden Gem

Most people know VLC for watching videos, but it’s also a powerful converter. No ads, no gimmicks, just open-source goodness. Perfect for those who want safe, offline solutions.
4. Online Audio Converter (123Apps) – Best for Simplicity
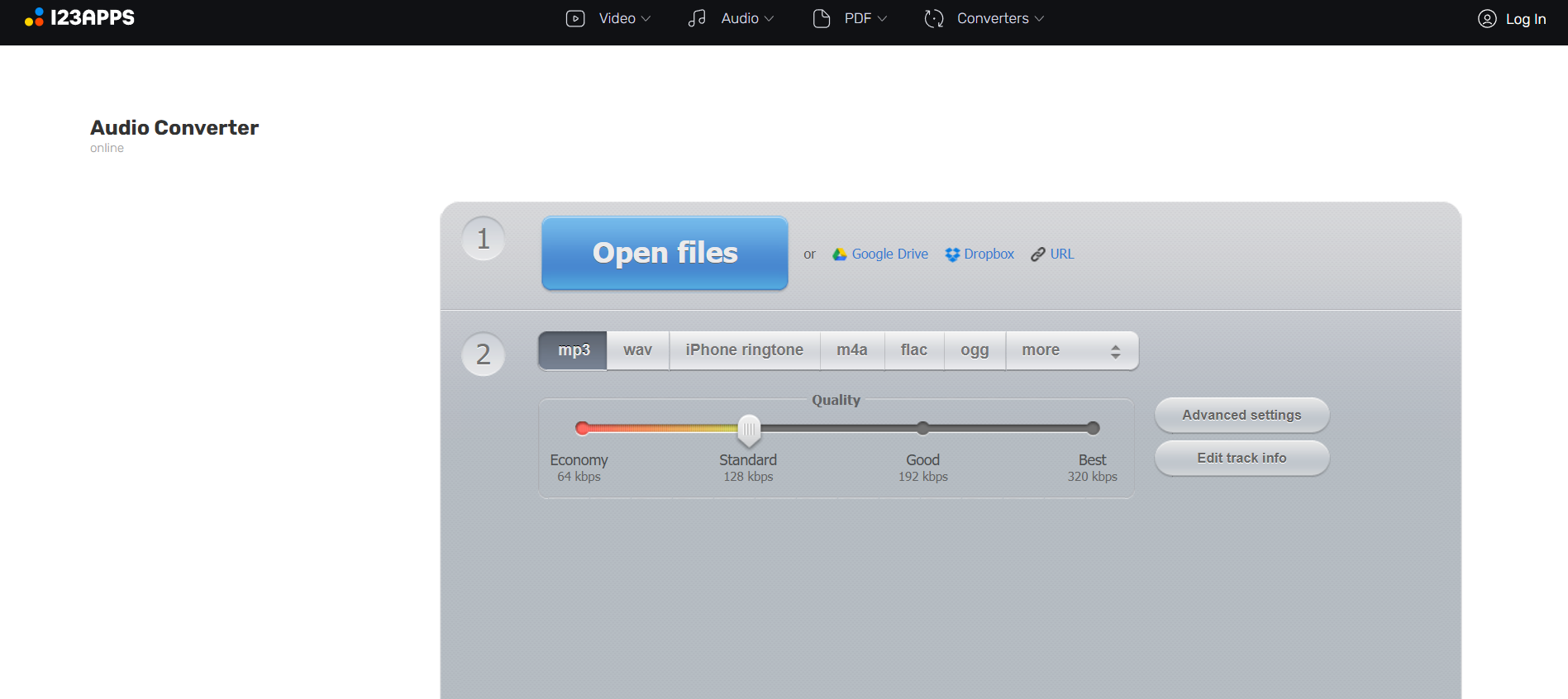
Online Audio Converter – Super easy to use. Upload your FLV file, pick MP3, and you’re done. It even supports trimming and adjusting bitrates before exporting.
5. Freemake Video Converter – Best for Customization

Offers lots of conversion options. The free version is solid, though you’ll see a watermark on video (not on audio). Great for users who like extra control.
6. ClipConverter.cc – Best YouTube to FLV MP3 Tool
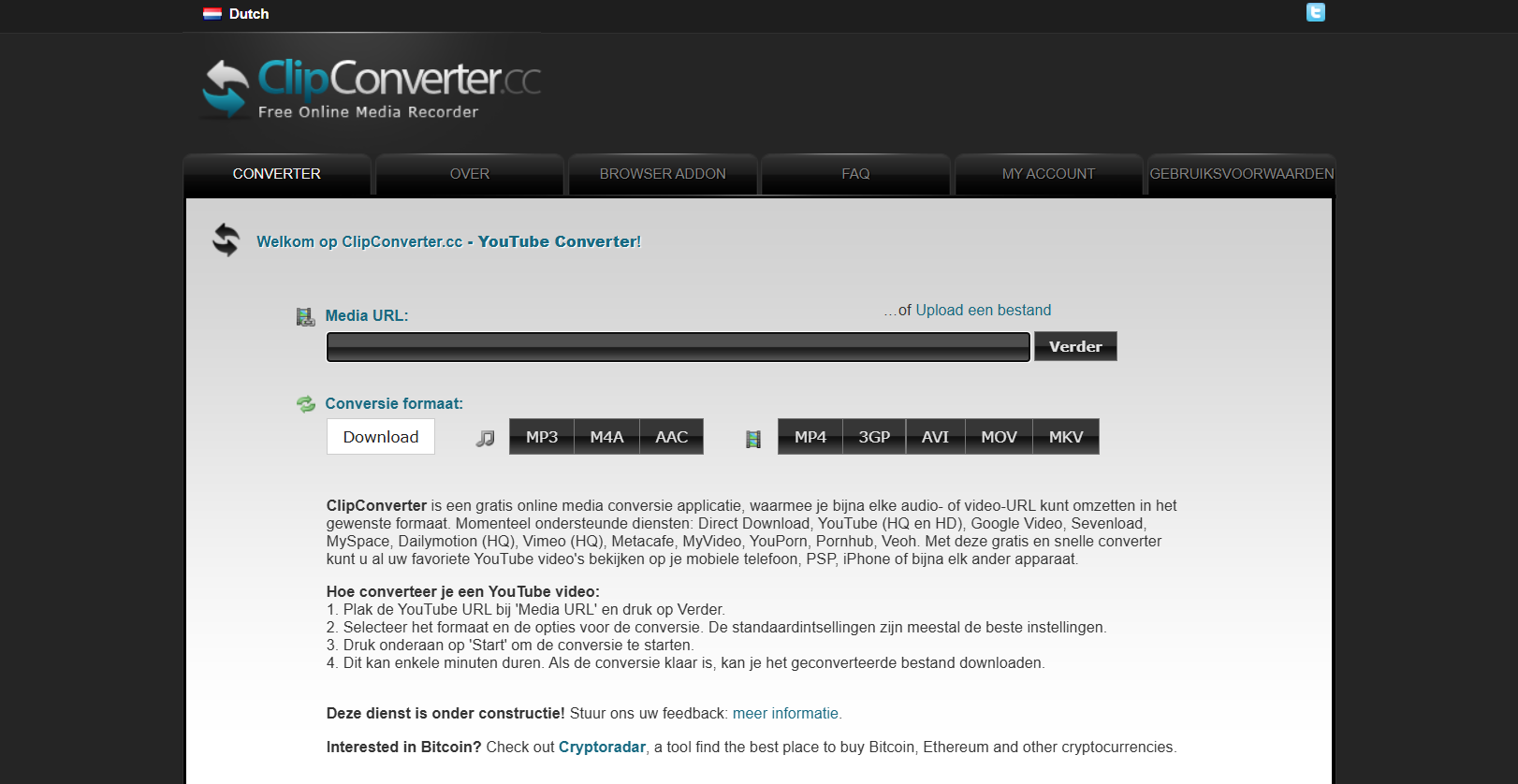
If your FLV file comes straight from YouTube or other video platforms, ClipConverter makes it super easy. Paste a link, choose MP3, and download instantly.
7. Convertio – Best Cloud-Based Converter
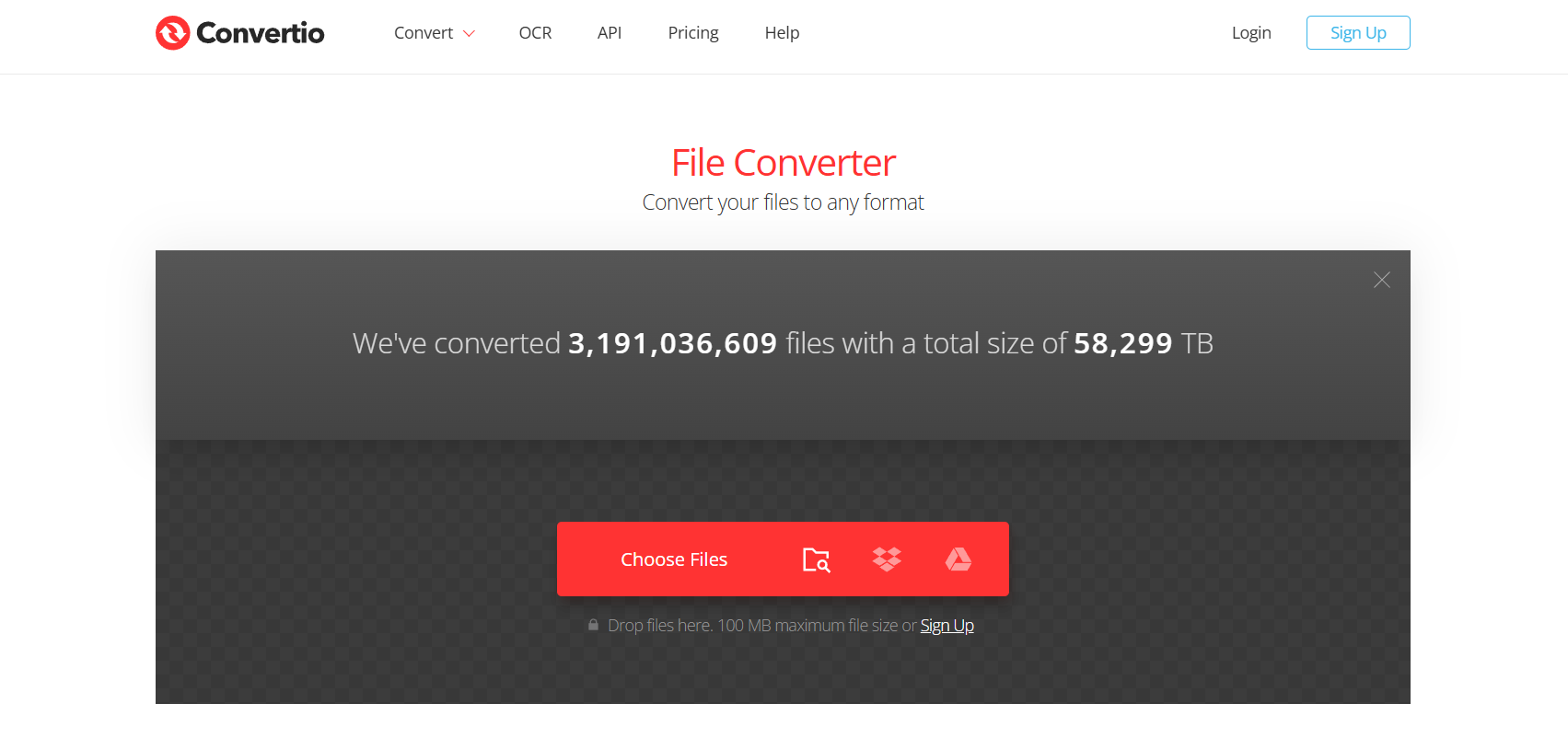
Works entirely online and even integrates with Google Drive and Dropbox. Perfect for people who store files in the cloud and don’t want to move them around.
8. MediaHuman Audio Converter – Best for Bulk Conversions
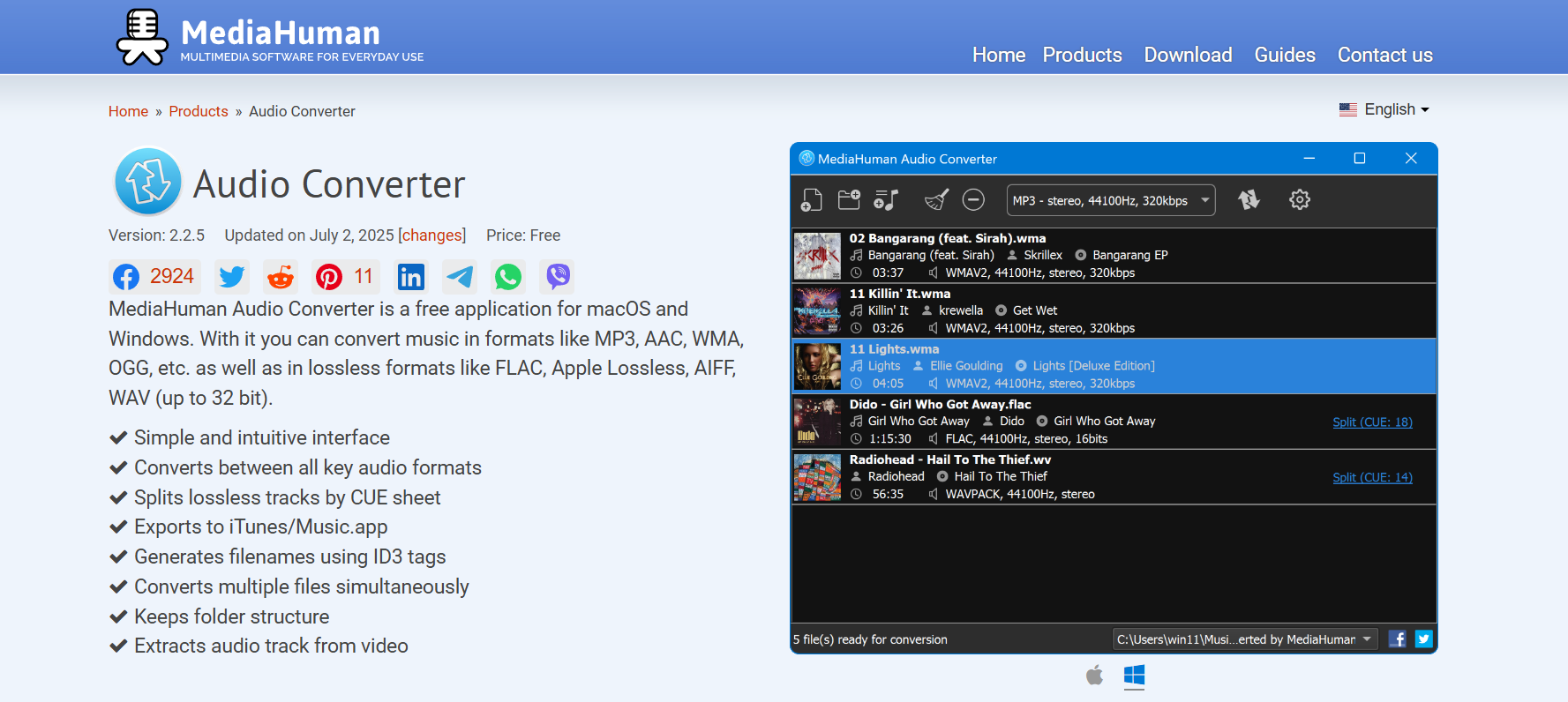
If you’ve got dozens of FLV files, this tool can handle batch processing easily. Drag multiple files in, walk away, and come back to a ready MP3 folder.
9. Zamzar – Best Multi-Format Online Converter
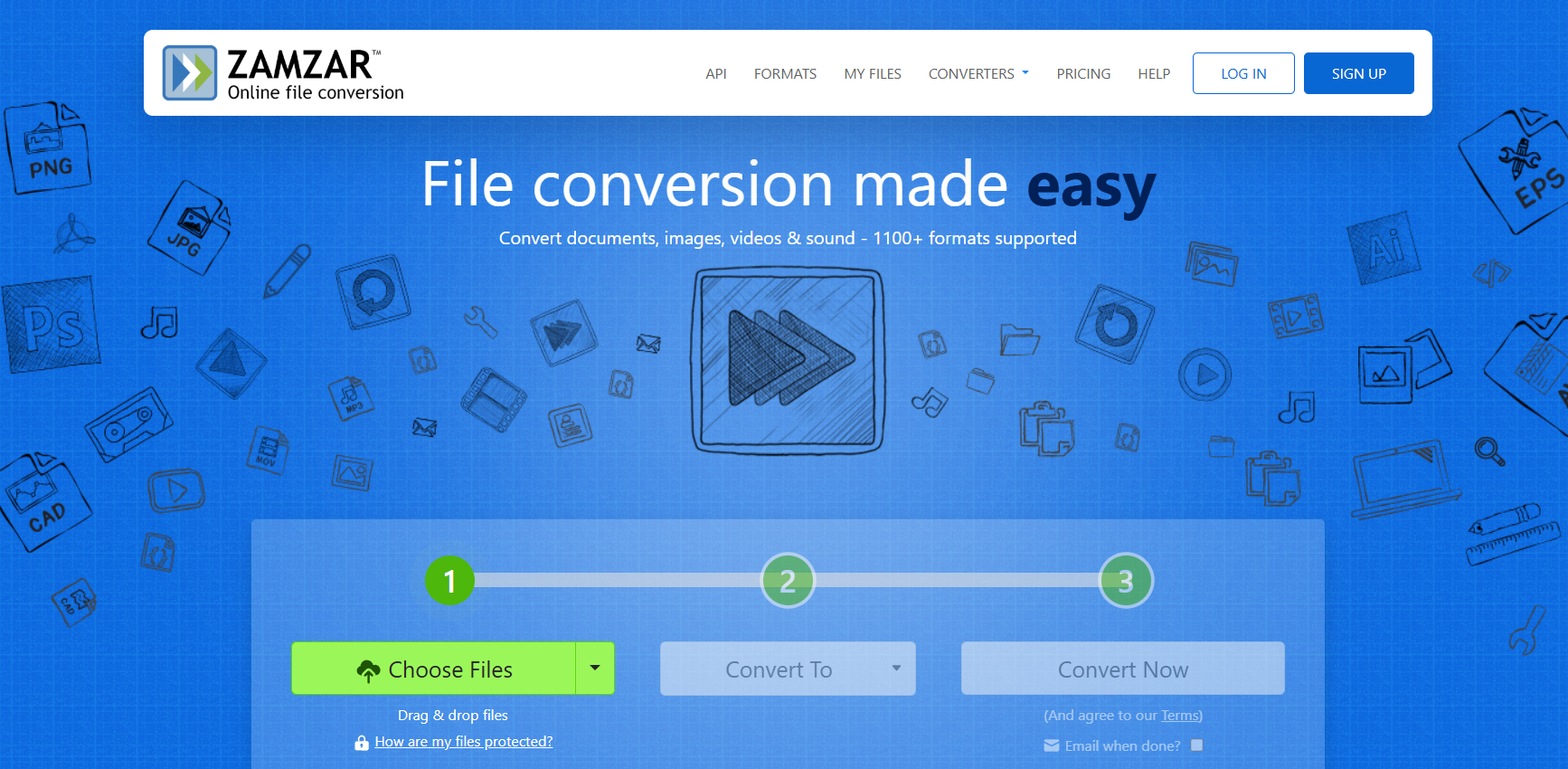
A long-time favorite for https://www.mediahuman.com/audio-converter/. Reliable, simple, and sends download links directly to your email.
10. MP3Toolbox – Best Lightweight Converter
Quick, no-frills, and works well for small FLV files you just want to extract audio from without overthinking.
Step-by-Step Guide: How to Convert FLV to MP3 Easily
Method 1 – Using Online Converters
- Go to a site like OnlineVideoConverter or 123Apps.
- Upload your FLV file from your computer or phone.
- Select MP3 as output.
- Adjust audio quality settings if available.
- Download your converted file directly to your device.
Method 2 – Using Desktop Software
- Open VLC or Any Video Converter.
- Add your FLV file by dragging it into the app.
- Choose MP3 as output and set the bitrate.
- Start conversion and save it locally.
Method 3 – Converting on Mobile Devices
Many tools like Convertio or ClipConverter work directly in mobile browsers. Just upload and convert. Some even let you save straight to cloud storage or music apps.
Common Mistakes to Avoid When Converting FLV to MP3
Choosing Low-Quality Converters
Don’t waste time on spammy sites that add malware, pop-ups, or low-quality audio. Stick with trusted names.
Ignoring File Security and Privacy
Be cautious if you’re uploading personal files. Always read the privacy policy and avoid shady websites.
Overlooking Batch Conversion Options
If you’ve got lots of FLV files, don’t convert them one by one. Use batch converters like MediaHuman or Any Video Converter to save time.
Forgetting About File Size Limits
Some online converters have strict file size caps. If you’re working with large videos, desktop apps are better.
Conclusion – The Best Way to Convert FLV to MP3 in 2025
Converting FLV to MP3 doesn’t have to be complicated. Whether you need a quick flv to mp3 converter online like OnlineVideoConverter or a powerful desktop tool like Any Video Converter, the options above cover all needs. The key is knowing your priorities: do you need speed, quality, or the ability to handle many files at once?
If you want the easiest route, stick with OnlineVideoConverter for quick jobs, or VLC for a safe, offline option. If you’re working with a large media library, MediaHuman or Any Video Converter will save you hours. Try one today and make your workflow smoother.
Find More: Boost Your Sales With SEO Services
FAQs
1. Is converting FLV to MP3 legal?
Yes, as long as the content you’re converting is yours or not copyrighted. Converting pirated content for distribution is illegal.
2. Do free FLV to MP3 tools reduce audio quality?
Some do, but most of the ones listed here offer high-quality output with adjustable bitrates.
3. Can I convert FLV to MP3 on my smartphone?
Yes, tools like Convertio and ClipConverter work on mobile browsers. Some apps in app stores also handle FLV to MP3 directly.
4. What’s the safest FLV to MP3 converter in 2025?
VLC Media Player is the safest since it’s open-source and works offline. OnlineVideoConverter and 123Apps are safe choices online.
5. Are there any limits to using free converters?
Yes, many online tools limit file size or the number of conversions per day. Desktop apps like Any Video Converter don’t have these limits.
6. Can I edit audio while converting FLV to MP3?
Some tools like 123Apps let you trim or adjust audio before exporting. For advanced editing, pair your converted MP3 with software like Audacity.